Dusun IoT has both Bluetooth Long Range Gateway and BLE Beacon as Bluetooth long-range solutions. This article is going to tell you what is Bluetooth Long Range. The BLE Long Range mode is also known as coded PHY in Bluetooth protocol for a narrow definition. Both Bluetooth long range gateway and beacon devices are built on the Bluetooth 5 protocol in coded PHY mode. So, how does BLE long rance come?
Due to the growth in demand for wireless protocol cover range, a new ‘long range’ mode has been introduced in Bluetooth 5.0 protocol. This mode is achieved by adding a coded PHY option in the physical layer, which would significantly increase the signal transmission distance with the price of the signal transmission rate.
BLE Long Range Technical Principle
In contrast to other wireless technologies, Bluetooth technology is intended to support a wide range of achievable ranges between two devices, giving developers a great deal of flexibility to create wireless solutions that best meet the requirements of their target use case. The following are some important factors that affect how far a dependable Bluetooth connection can reach:
Bluetooth PHY (physical layer)
- Radio Spectrum
- Receiver Sensitivity
- Transmit Power
- Antenna Gain
- Path Loss
With Bluetooth Version 5.0, a brand-new PHY called Coded PHY was introduced. 1Mbps is still the transmission speed for raw data. However, depending on the configuration used, the rate is either 500 Kbps or 125 Kbps because of redundant user data in the data.
The effective user-data rate is ultimately less than the raw data rate because the data rates mentioned above also include packet overhead, headers, and other data. Instead of increasing transmit power, redundancy enables the receiver to use Forward Error Correction (FEC) algorithms to recover the original data from transmission errors.
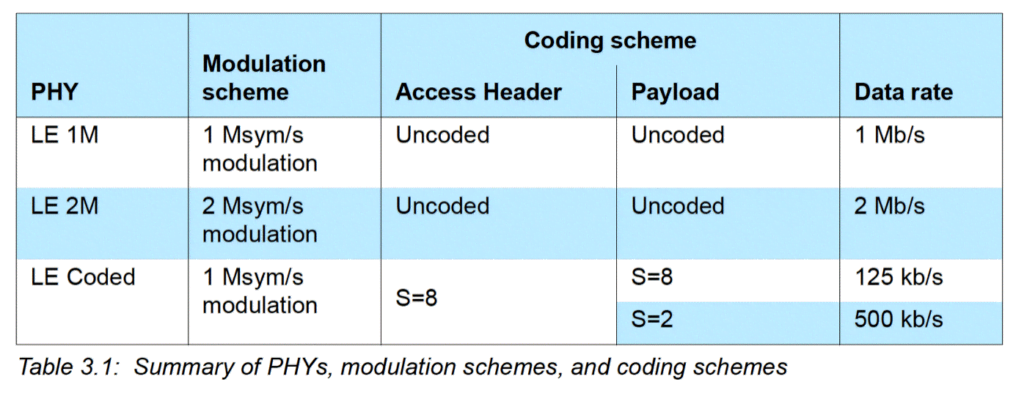
The likelihood of recovering data increases with redundancy. This is why the PHY rate is frequently expressed in terms of mega symbols per second. The various PHYs and rates offered by Bluetooth version 5.0 and later are as follows:
Original 1M PHY
1 Mega symbols/second –> where each data bit is represented by 1 symbol –> 1 Mbps
Coded PHY
1 Mega symbols/second –> where each data bit is represented by 2 or 8 symbols –> 500 Kbps, or 125 Kbps
2M PHY
2 Mega symbols/second –> where each data bit is represented by 1 symbol –> 2 Mbps
And here’s a table summarizing the differences:
A Different Coded PHY BLE Packets Format
However, Coded PHY BLE packets have a different format than the standard 1M or 2M PHYs.
Let’s take a look at the packet format:
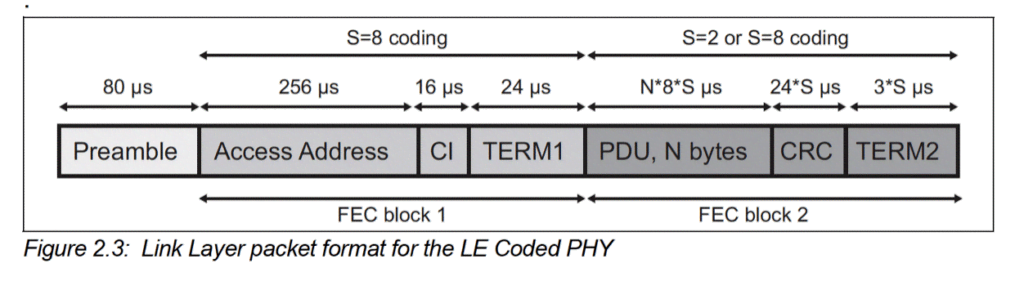
Important Notes About the Format
The Preamble is never coded, which allows the packet to be detected in any mode (Coded PHY, 1M PHY, or 2M PHY) before determining which mode was used for the remaining packet’s data.
FEC block 1 is always coded with S=8,
FEC block 2 is coded with S=2 or S=8 (depending on the configuration).
The CI (Coding Indicator) is used to indicate which coding scheme is used in FEC block 2 (S=2 or S=8).
The timing values show how long it takes to transmit the specific field within the packet.
Here’s a table that shows the size and duration of each of the fields within the packet (taken from the Bluetooth 5.1 spec):
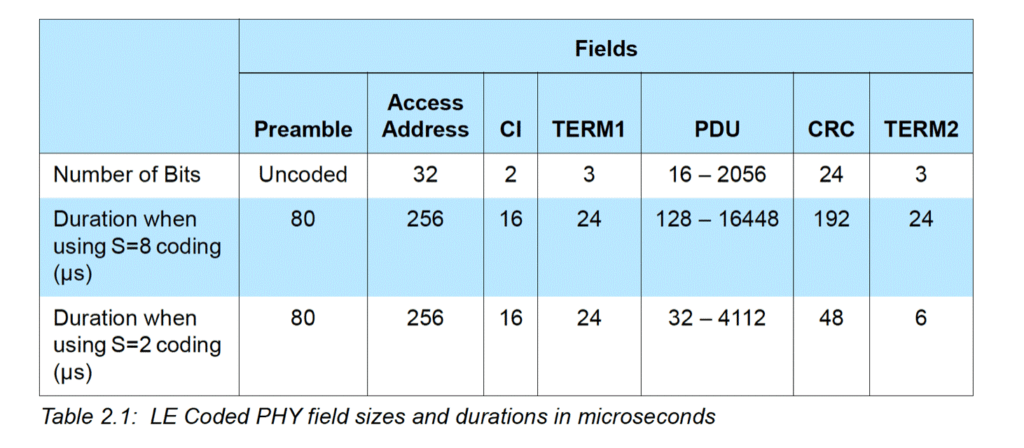
Source: Bluetooth version 5.1 Core Specification document
The table shows the differences between using S=2 and S=8 for coding. Notice how the choice impacts the radio-on time, impacting power consumption.
BLE Long Range Examples In Dusun IoT
Bluetooth Long Range Gateway
The DSGW-030-BLE is an IoT gateway hardware that is used in smart homes, intelligent security, and pension services.
It is a central device that supports multiple wireless protocols, including Wi-Fi and Bluetooth Low Energy (BLE 5.2). The Bluetooth gateway also has an easy-to-use interface that allows you to easily configure the entire system and integrate the Dusun IoT hardware with your system.

Bluetooth Beacon
DSBC-150/151/152/153 is a Low Energy wireless beacon or sensor beacon that can detect motion, collect ambient temperature and humidity, and more. Some products feature iBeacon/Eddystone functionality, a high protection level (IP66/IP68), and a small footprint, lightweight, portability, and pinpoint accuracy, making them suitable for applications across the board in areas like cold chain logistics, archives, laboratories, museums, and more.

How to Install and Deploy Bluetooth Long Range Gateway
Customers can log into the Dusun Bluetooth Long Range Gateway’s Luci browser to configure the gateway and obtain the data. User can configure the data report format from Format data to RAW data following the steps below:
- Data Type: Raw Data or Format Data;
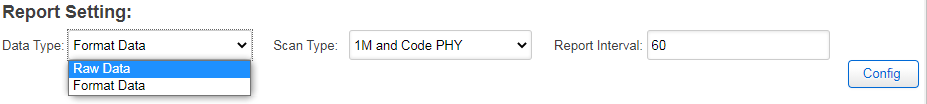
2. Scan type, vary from 1M to Coded(long range) PHY;
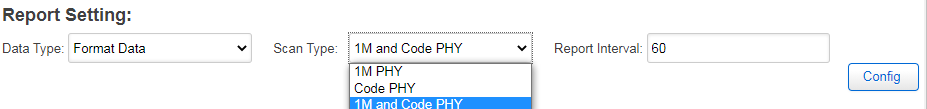
3. Report interval: time gap for ble list to be reported;
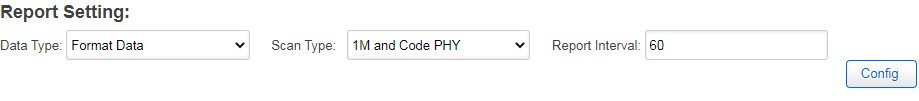
4. Users can configure the filter section to obtain information from the desired devices only.

Why Choose Dusun IoT’s BLE Long Range Gateway and Beacons
As a purpose of extending the cover range of the Bluetooth scanning system, Dusun IoT provides both BLE beacons and Bluetooth gateways with the latest generation BLE 5 stack installed. As a result, the entire system could transmit data in coded PHY (long-range mode). Compared to a traditional 1M PHY system, the cover range of our BLE long range hardware devices could be increased by at least twofold. Several different methods listed below:
Higher Transmit Power
Dusun installed a power amplifier in each BLE beacon designed for a wide coverage area, which increased the transmit power (TX) of the beacons from 8dbm to 19dbm.
Higher Sensitivity
The Bluetooth chip embedded in the Dusun Bluetooth gateway is a new generation series from Silicon Labs with high sensitivity.
Open Source
Dusun IoT’s products are open source, and customers can carry out secondary development on this basis to meet individual needs.
Quality Assurance
With both Bluetooth and BQB certifications under our belts, you can rest assured that your purchase of one of our IoT products will be of the highest quality.